Wishlist/Anti-Theft Mode
From Openmoko
| Wishes warning! This article or section documents one or more OpenMoko Wish List items, the features described here may or may not be implemented in the future. |
This page presents details for this blueprint.
Suppose you are in a busy environment and your device is lying around somewhere. You sometimes use it but cannot look after it all the time. A sort of high risk environment for phone theft where you could put it in anti theft mode which is goes into an alarm mode when a custom user selection of the following occurs:
- someone moves it
- someone touches the touch screen or presses a button
- someone removes the USB/charging-plug
- removal of Bluetooth/WiFi devices in vicinity
- some special code is received by SMS
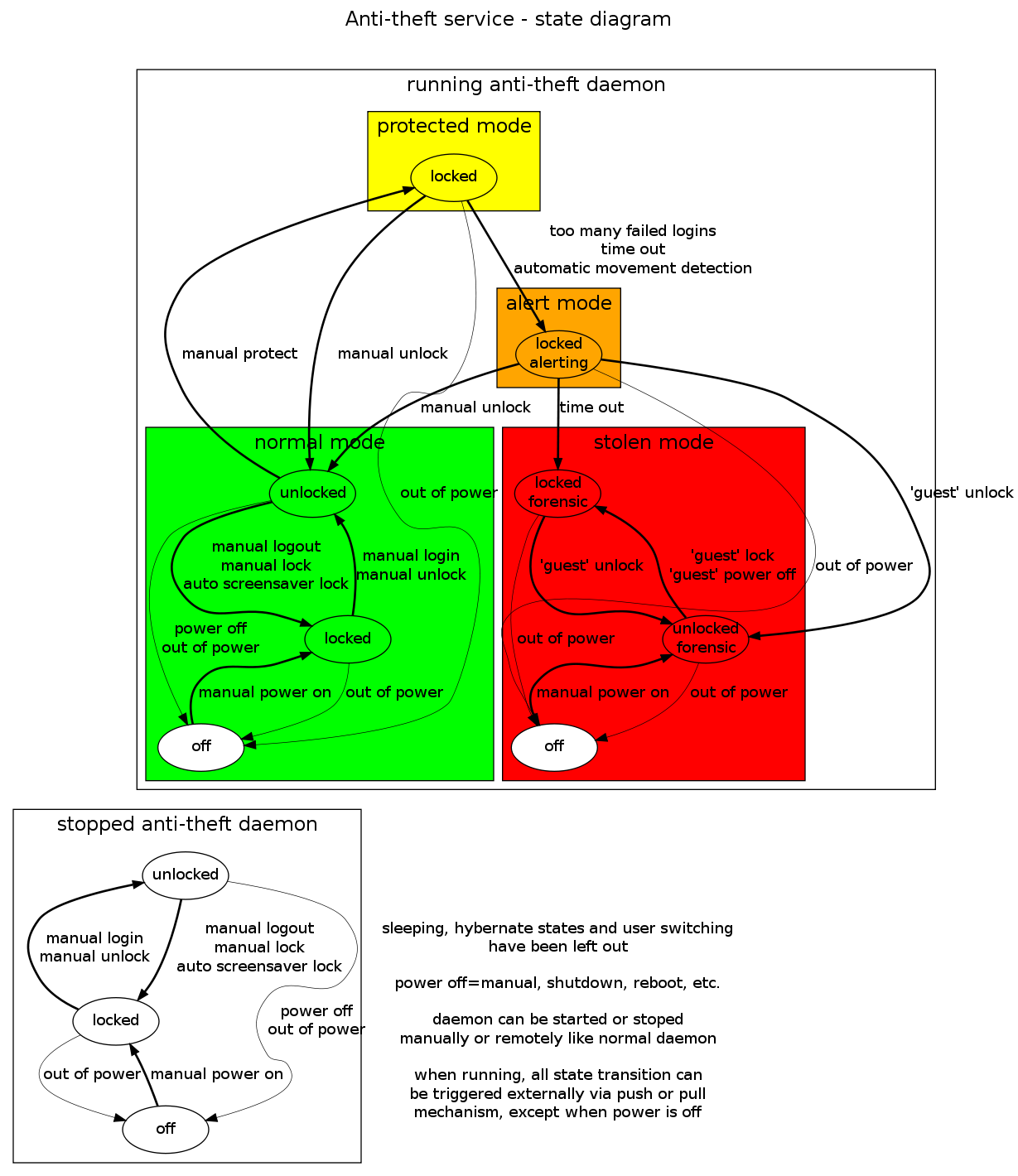 This alarm mode can be switched off by:
This alarm mode can be switched off by:
- entering a password/pin (custom user selection for prompted or unprompted interface)
- doing a certain gesture (measured by accelerometers or touch screen)
- voice verification ;-)
- image recognition
- remote-reactivating (USB, WiFi, Bluetooth, webservice on the device)
- mixture of the above
From the moment it has been moved or touched':
- it will display a warning on a red background flashing in black: You are committing a crime. Put this phone back, now! (or similar). Make sure is it a positive stimulus for the perpetrator.
- do nothing. It may simulate a fake network error or similar when a number is dialed. It may provide limited functionality so that the device is not thrown away as trash or users data is being accessed or high costs are being generated.
If it is not unlocked after predefined number of seconds may:
- set off a loud alarm
- start sending messages to a predefined email address with live data like pictures from the camera, audio recordings from the microphone, GPS coordinates, logs of numbers dailed, URLs surfed to and messages send, WiFi network and USB ID's for retracing the location of the device and identifying the perpetrator. (Compress the attachments of the email.)
- activate self-destruct mechanism
If the above anti-theft measures fail
- a special text message could be sent to the phone which erases all contacts then activates the pin lock for the phone and SIM card.
- activation of some sort remote control
In addition. If you've put it down and forgotten about it, somebody picks it up, it would first ask for the PIN, with a message on-screen that says something like "If you don't know PIN, give 1234".
If user types 1234 then it presents 2 buttons: "Contact owner of phone" and "Use phone" (==I'm stealing this).
If user selects "Use phone", then it would present factory looking interface with empty of fake address book, etc. and quietly contact owner anyway and tell current coordinates ;-) Also logging of text input will be activated and emailed to the owner.
The idea is keep the thief using the phone until the police arrive and recover it. If phone notices new SIM, it would go directly to "I'm stolen" mode. Maybe run under Linux-VServer http://www.linux-vserver.org/ in stolen mode.
Perhaps, assuming the phone was locked in such a manner and later found or recovered by police, the phone could be returned to "normal mode" by entering the pin AND being within 100 meters of a "home" location, defined by the GPS when you first set it up.
With suitable arrangement remote ssh connection to phone should be possible which would give nice control over stolen phone.
There could also be a bluetooth headset and/or bluetooth watch. If it loses contact to phone, phone would complain loudly and if bluetooth gadget is enough smart it could complain too. This gadget could warn about low battery too.
Implementation
Peeloo: How about using Adeona, an "open source system for tracking the location of your lost or stolen laptop that does not rely on a proprietary, central service." It'll surely need to be cutomized to require as less battery as possible, but the implementation is here, and seems to be pretty well though.
Pander: Good idea! I've noticed that is already being packaged for Ubuntu Linux.
Upload protocols
Since HTTP is the most commonly available and mostly allowed protocol on the Internet medium, this would be the primary protocol for uploading information via the Internet. For the mobile network medium, SMS with summarised information in a special encoding would be the protocol for uploading. Both media can be used simultaniously when available.
When not available, information will be stored and transmitted later in the following way. Send package t=now, send package t=0, send package t=now-1, send package t=1, package t=now-2, send package t=2, ... This increases data richness when the device is not continuously connected via that particular medium.